Introduction: The existing development of methods for ensuring information security in the field of information technology makes it possible to ensure the confidentiality of data of persons at variable levels. Hardware solutions can be portable cryptographic keys, as well as highly targeted biometric identification devices. The software solutions are static identification methods through sequences and side solutions for deploying data virtualization systems.
The main problem that stands out among the above methods is the need for additional hardware, acting as tokens, infrared cameras, biometric identification sensors. An alternative problem is the lack of security of software solutions, since the presence of zero-day vulnerabilities can reduce the security factor, which leads to the possibility of interception of confidential data by third parties. Purpose of the research: The purpose of the study is to analyze and implement software methods and algorithms to ensure data security based on containerization methods.
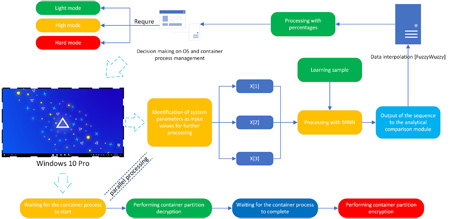
The developed software solution allows performing tasks of an application type in a secure container, while the implemented authentication methods support the ability to identify a person through sequences, authentication methods using the Windows Hello API. Methods: The investigated security methods and algorithms have made it possible to implement a unique cryptographic algorithm. Results: The methods and algorithms for the implementation of a limited shell obtained as a result of the study made it possible to variably select the optimal variations in the work of internal instances of the work of processes along with the implementation of cryptographic methods. Application software is based on the joint use of virtualization tools and methods of interaction through neural technologies. The isolation of this solution from alternative methods lies in the possibility of using a container without significant expenditure of hardware resources and lack of primary knowledge in setting up a software module. Practical significance: The practical significance lies in the possibility of using methods and algorithms in the construction of secure workplaces in small and medium-sized businesses.